corporate desktop under control
What is GECOS?
An installation media for desktops
A software catalog
One system to rule them all
An installation media for desktops
A DVD...
... or a pendrive.
GECOS v2 installs itself in 10 minutes, leaving the computer ready for the end user.
You can install hundreds, thousands, millions of times for the same license cost: 0.
It's Free Open Source Software

1:Installation
The base install is quite easy.
Download a GECOS disk image and burn it on a DVD or USB drive, boot the computer from it, and follow the instructions from the Install Assistant.
2:Attach
For remote management we'll attach the installed desktop to GECOS Control Center, and to an user authentication source (LDAP or Active Directory).
Run the Configuration Assistant.
This way for a closer look
1:Install
- Download GECOS disk image
- Burn the .ISO file to a DVD or USB drive and insert or plug it in the computer.
- Check that the computer will boot from DVD unit or USB drive

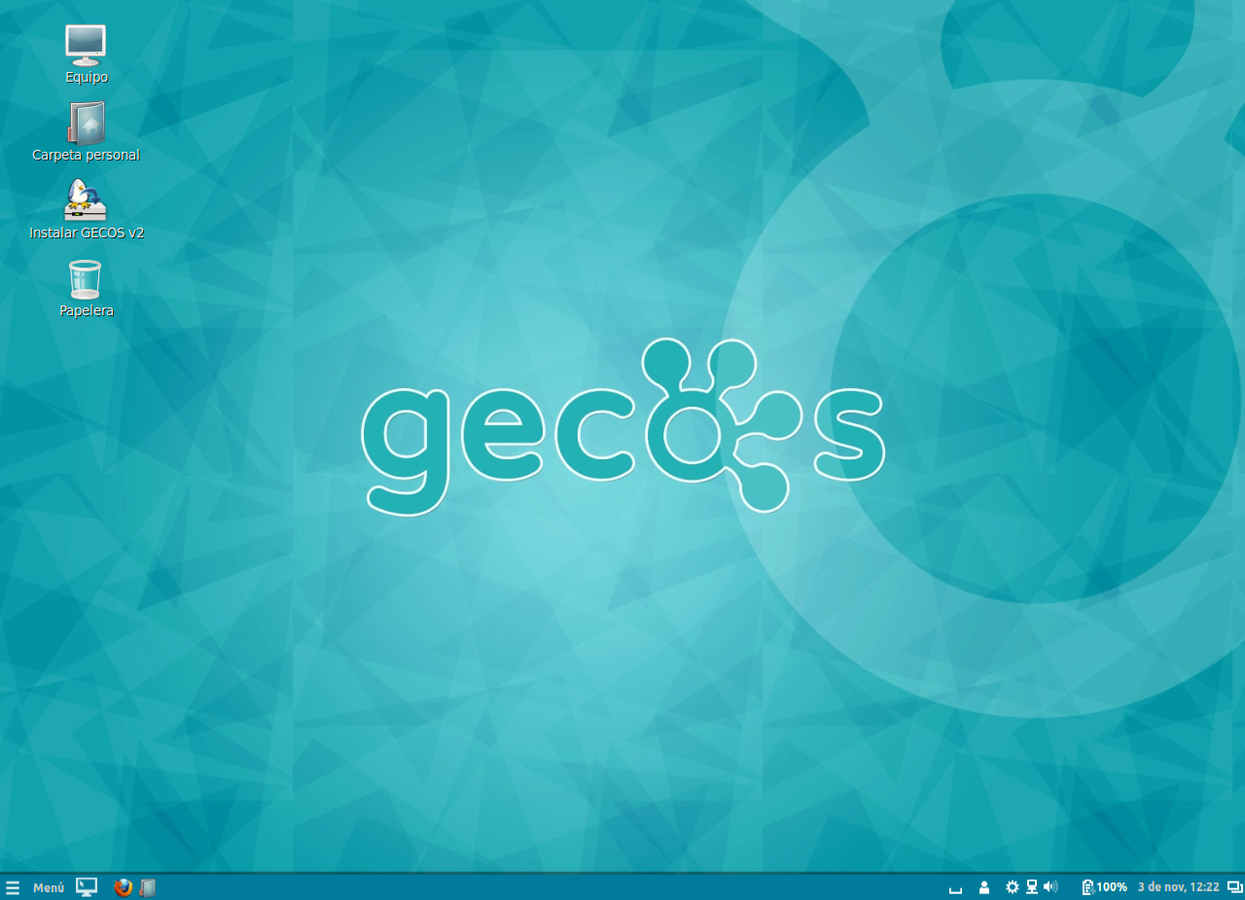
Wait a moment and...
... when the graphical desktop starts,clic on the Install GECOS v2 icon
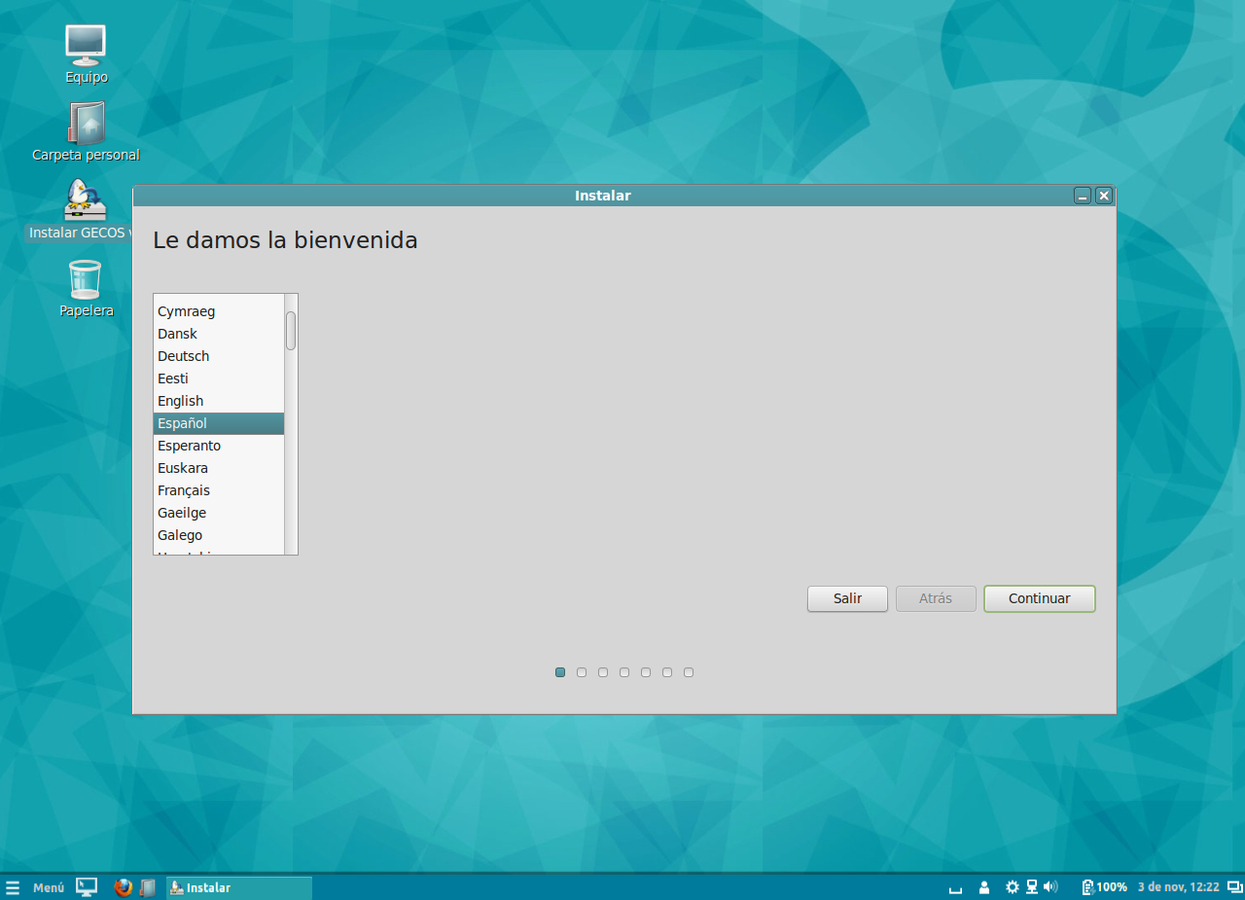
Choose your language
and press Continue
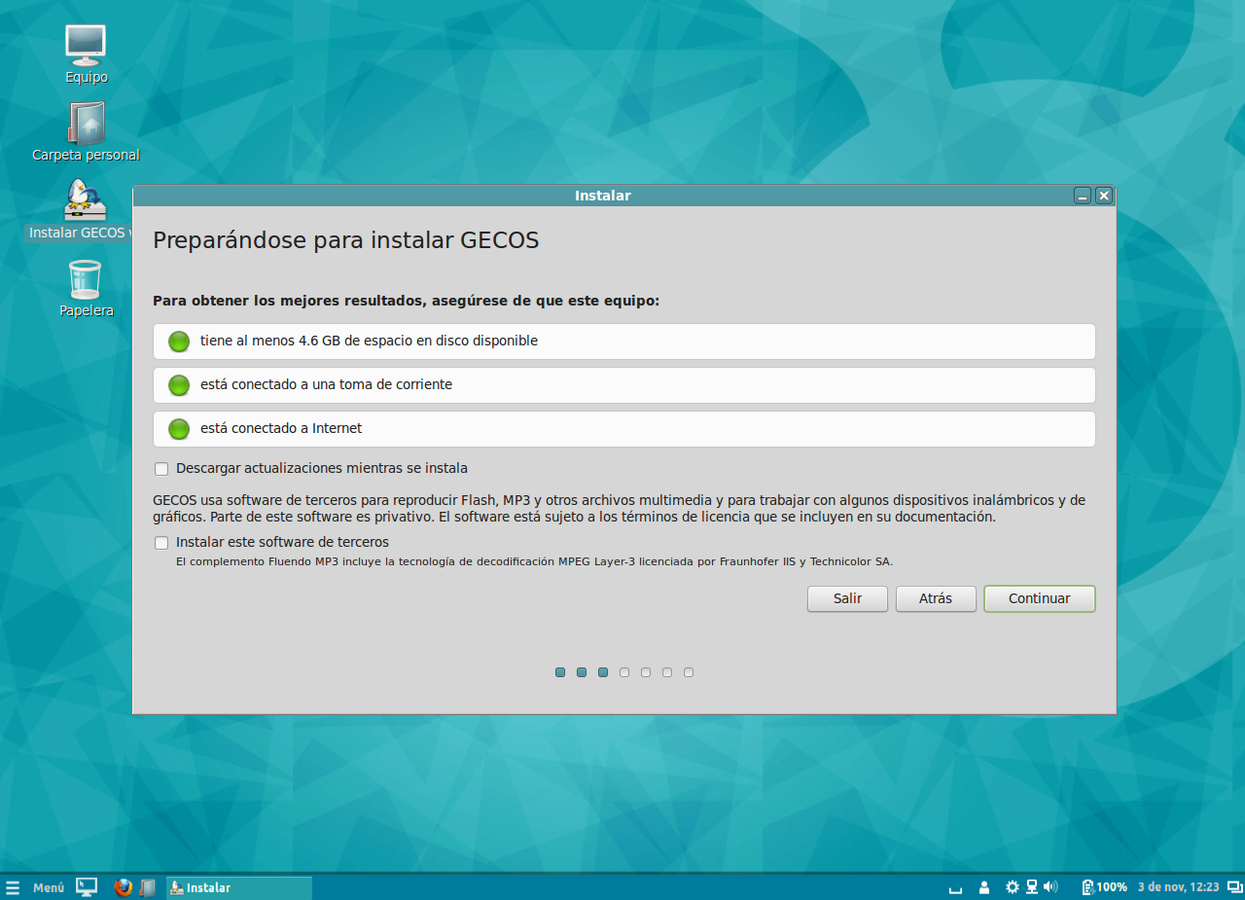
Check that...
- there's enough free disk space
- the computer is attached to the network
- it's plugged to a power supply (in case of a laptop)
and press Continue
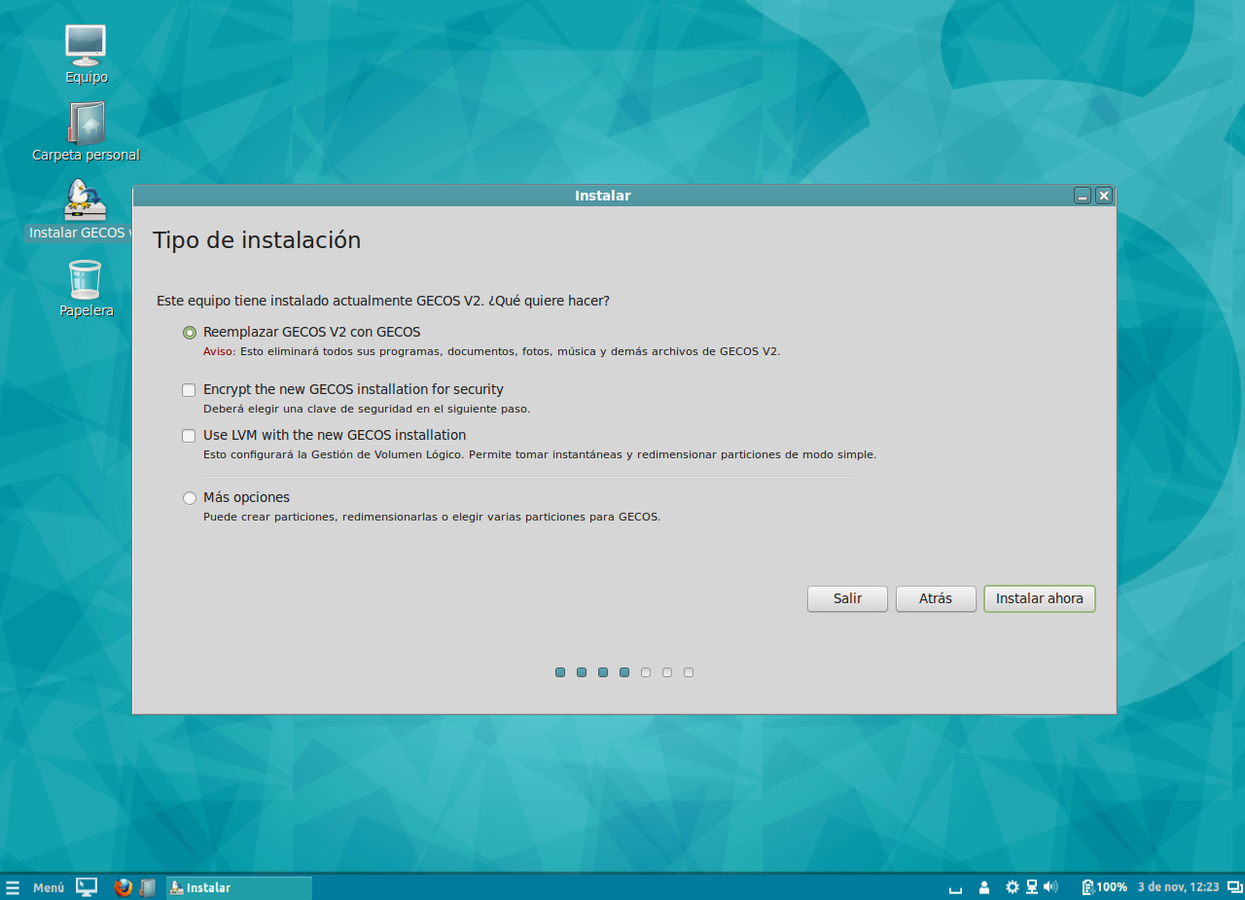
Select a place
for GECOS in your computer.
You can have GECOS as the only Operating System or use several O.S. in the same computer.
At this point, you can create, delete or modify any disk partition.
Press Continue
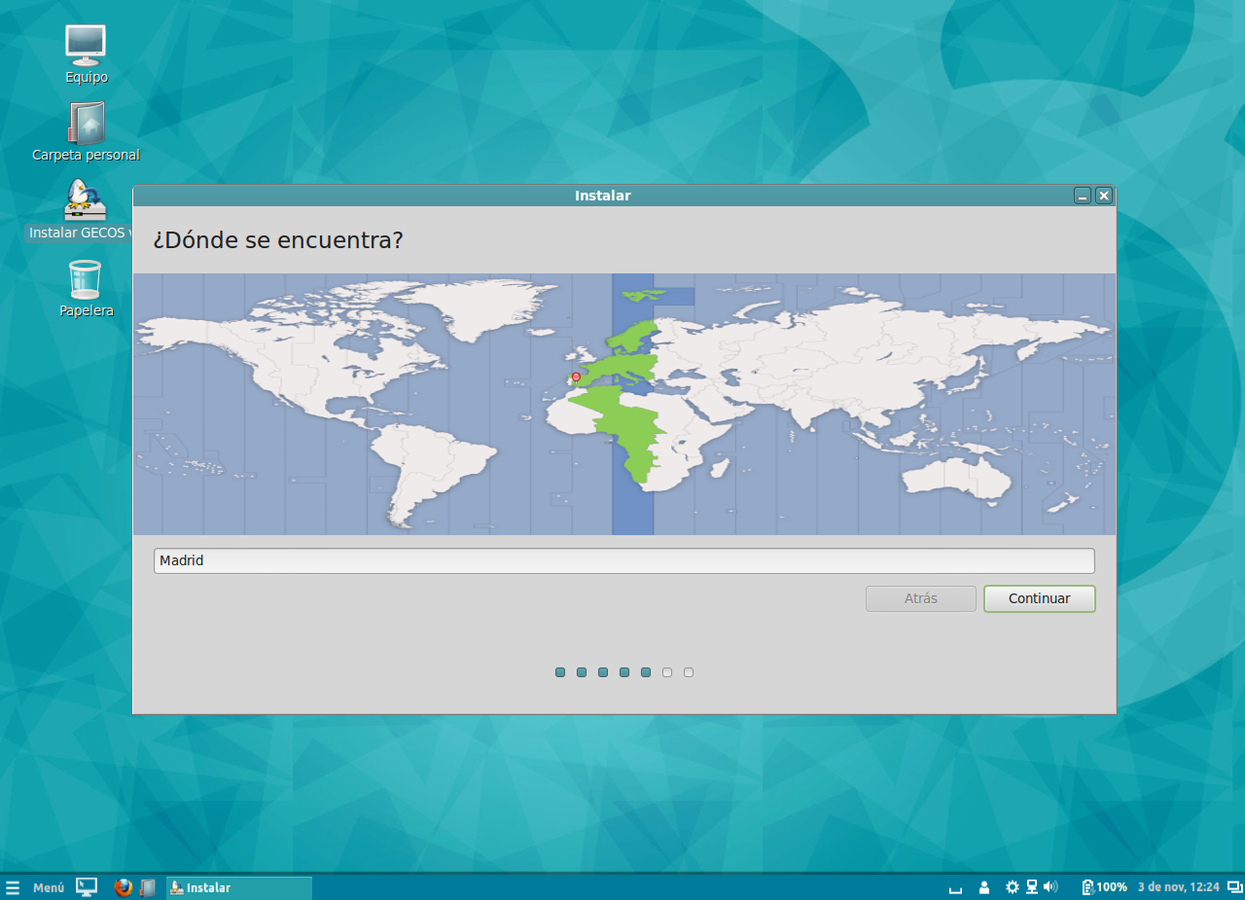
Time Zone
The installer guesses from your Internet connection, but you can change it.
Press Continue
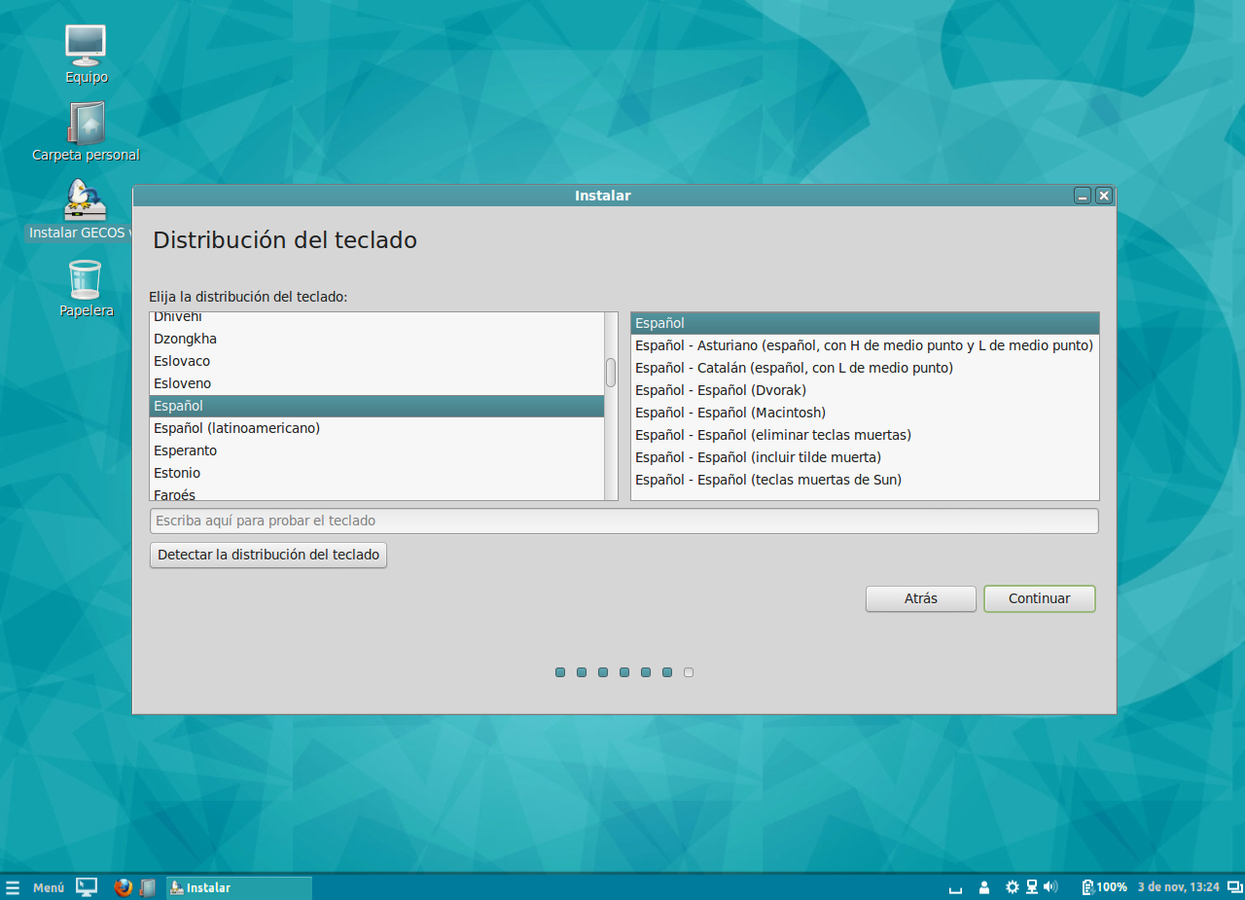
Keyboard selection
Probably you won't need to change this.
Press Continue
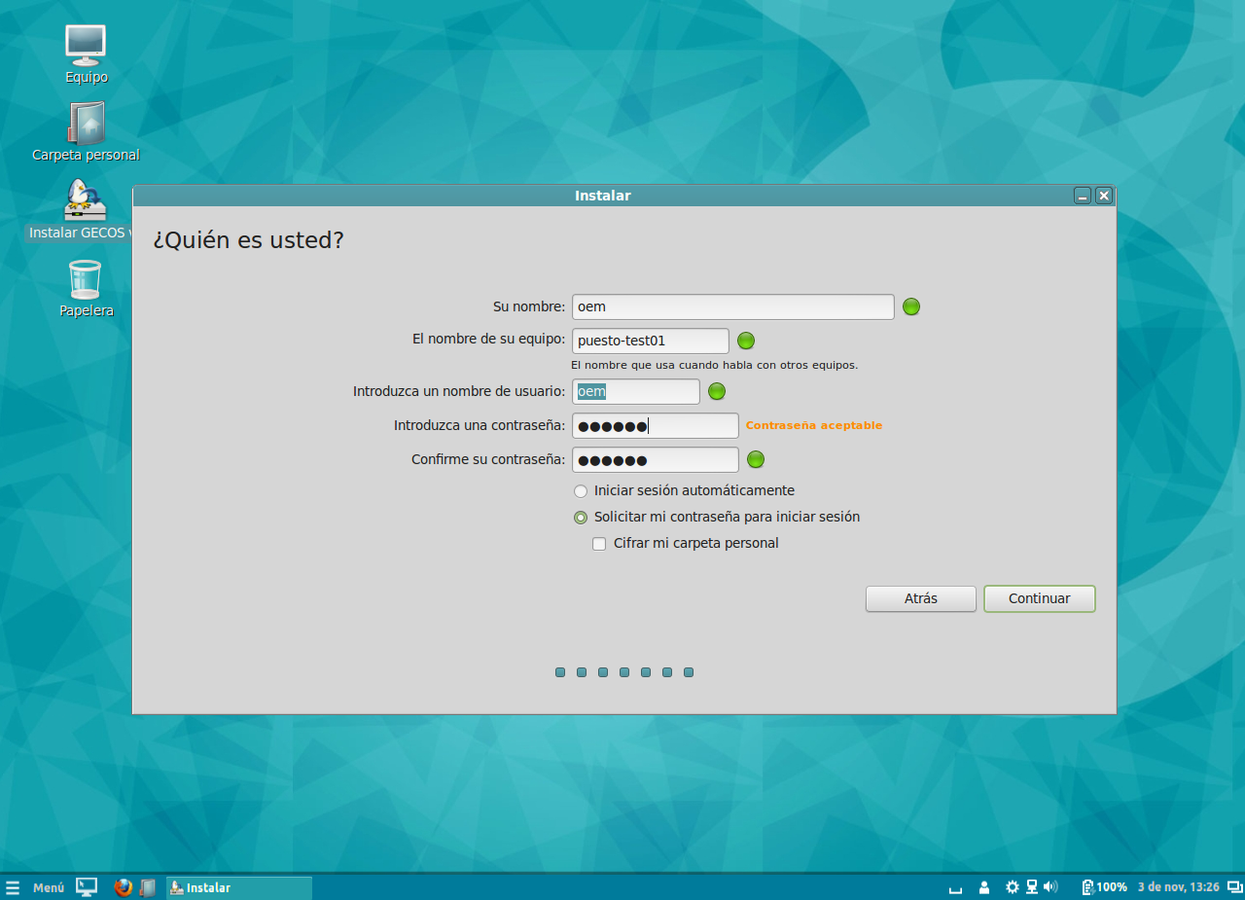
Identity Form
These are basic data items needed for the installer to configure your desktop.
The user and password in this form will allow you to log in for the first time, please write them down.
Press Continue one more time.
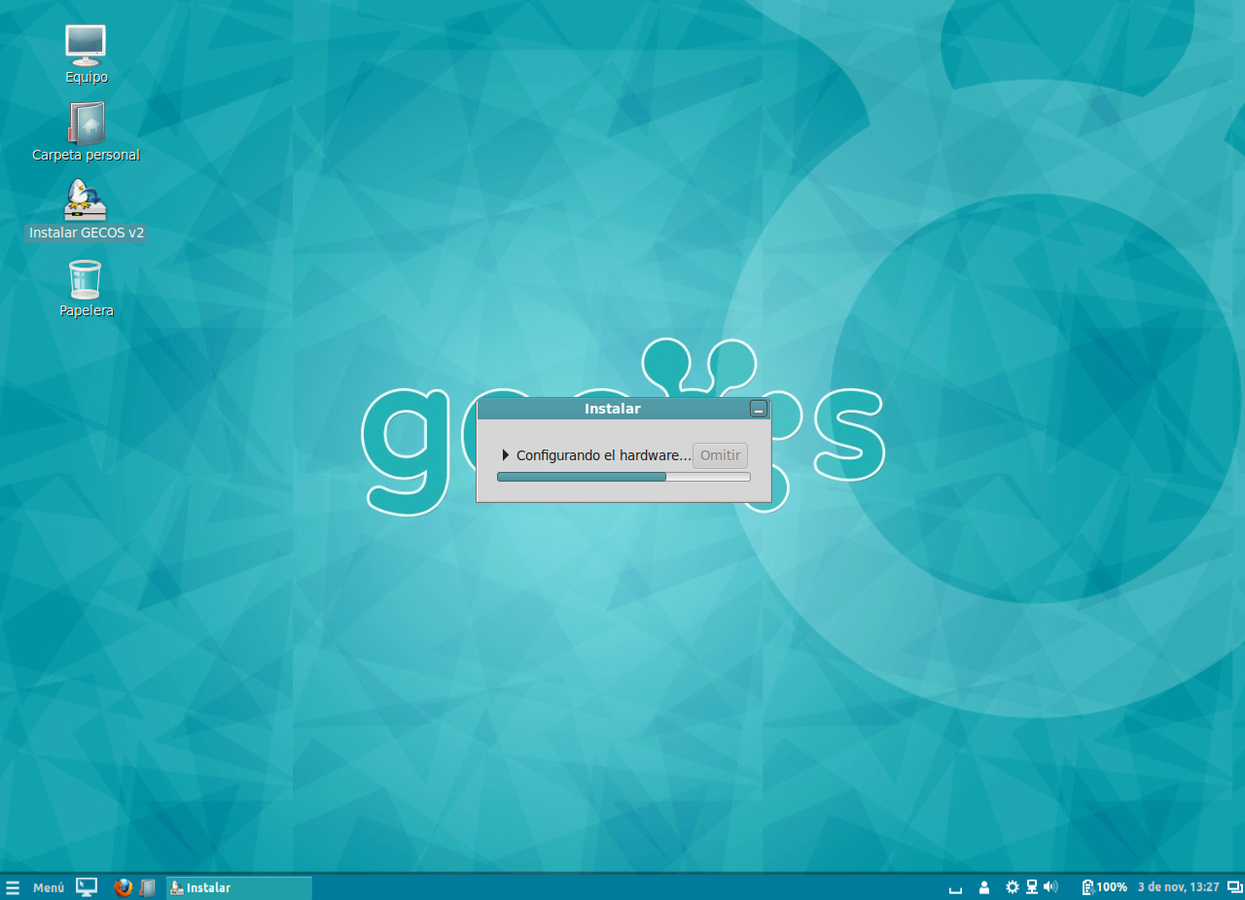
That's all
Wait for the installer to do it's job.
Normally it takes only five or ten minutes, but it depends on the DVD or USB drive and hard drive speeds.
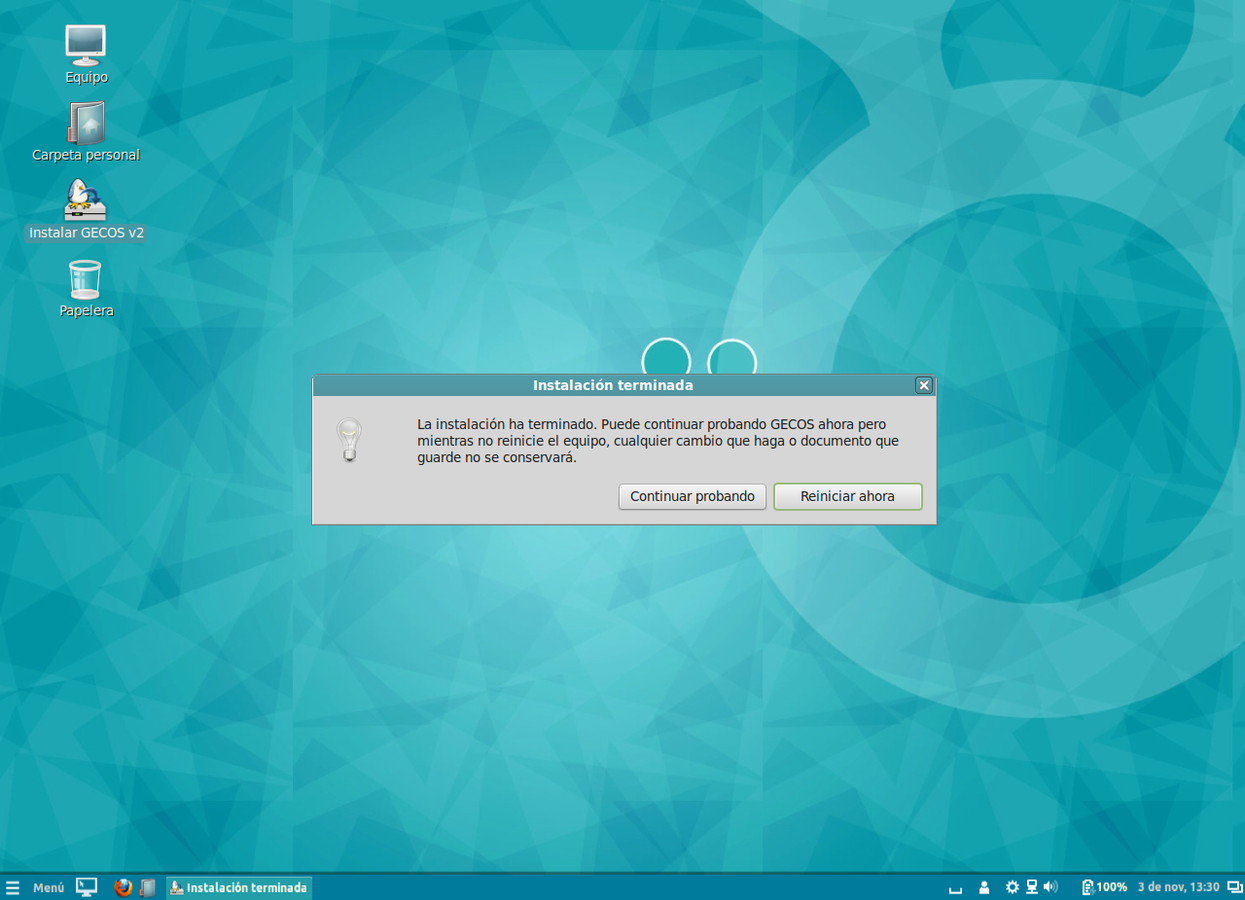
The end!
Installation is over.
Reboot your computer and don't forget to remove the DVD or USB drive.
Now you should attach the newly installed computer to a GECOS Control Center.
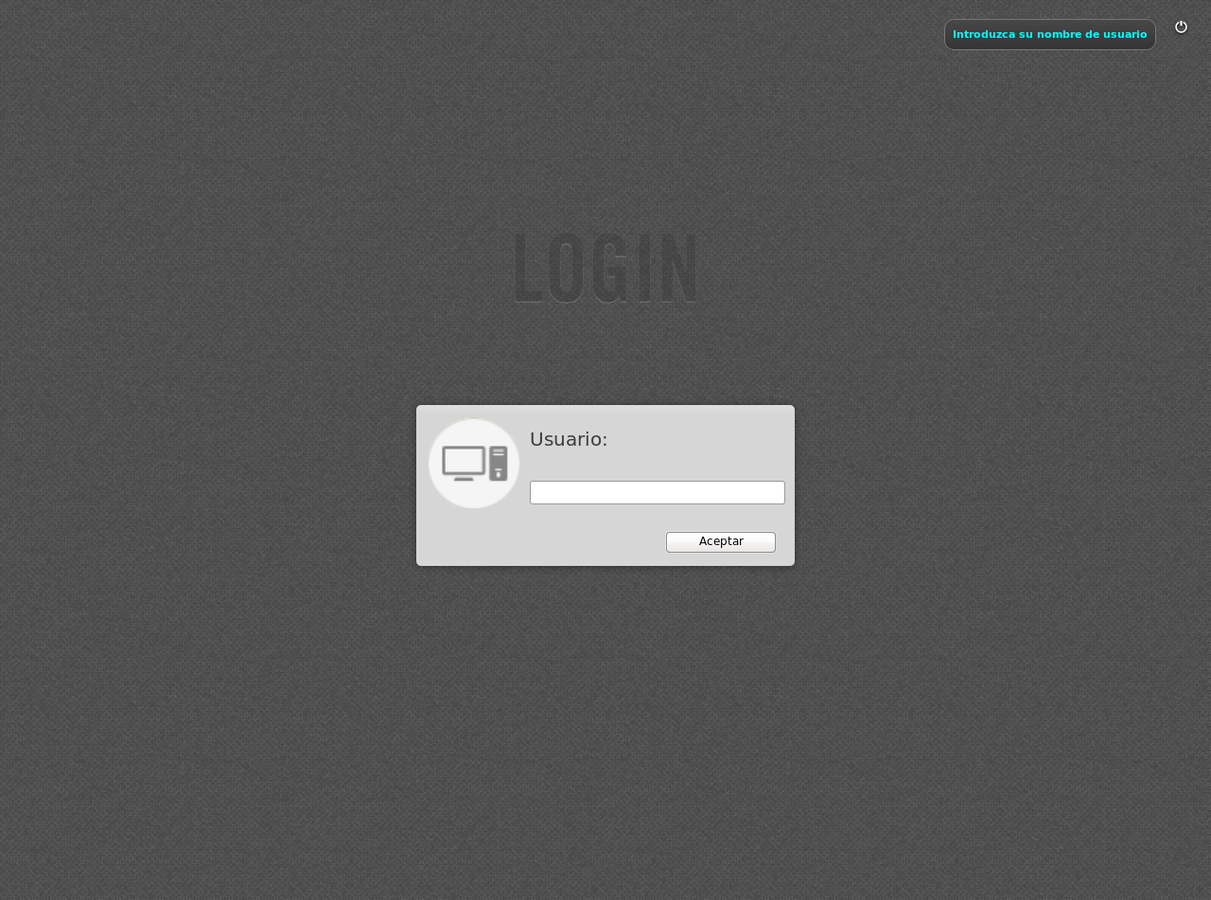
Log in to the computer.
You'll need the user and password you typed during installation.
2:Attach
G.C.A.
or GECOS Config Assistant, will guide you step by step in order to attach the computer to GECOS Control Center
Only superusers, as the user created during the installation, can run G.C.A.

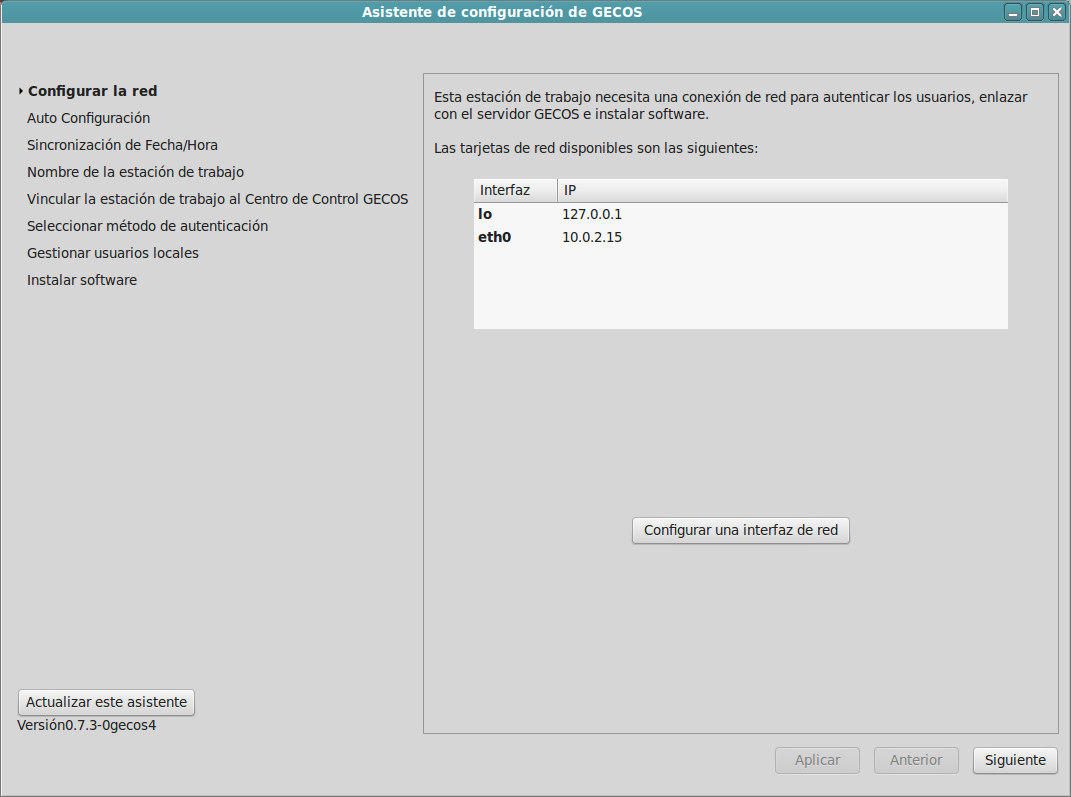
Network connection
Your network connection should be properly set up, check it.
Press Next
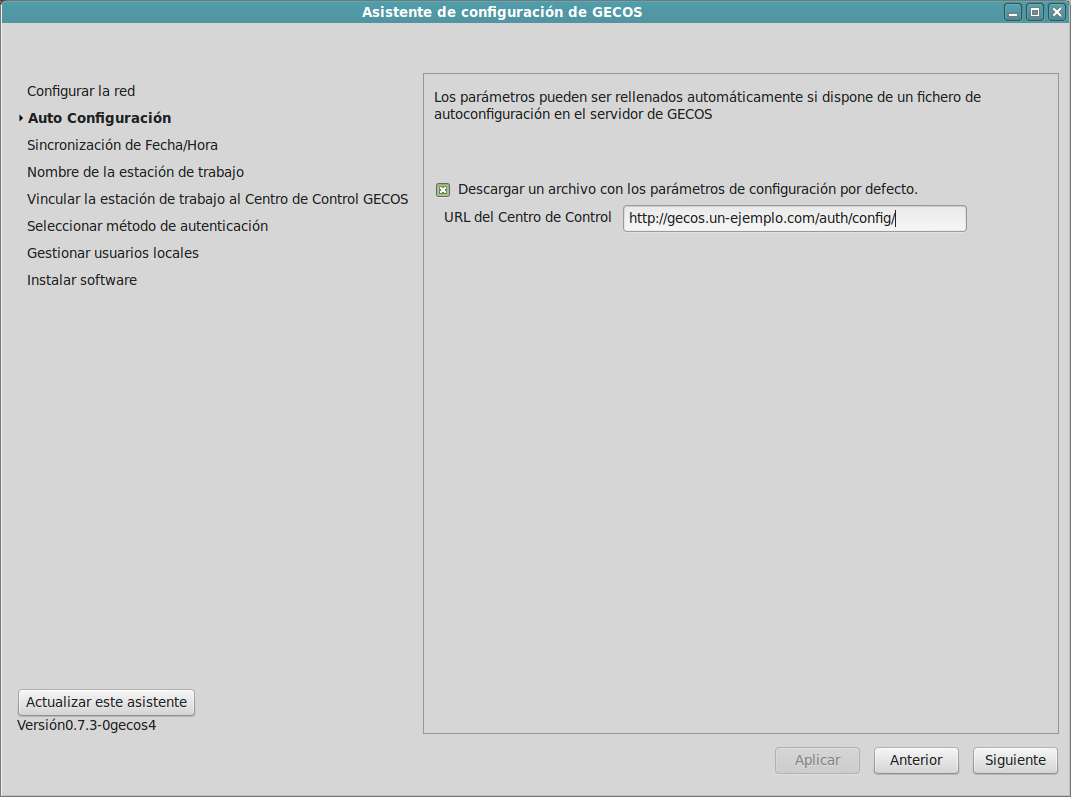
Make it faster and easier,
download configuration parameters from the Control Center.
You only need to remember one URL.
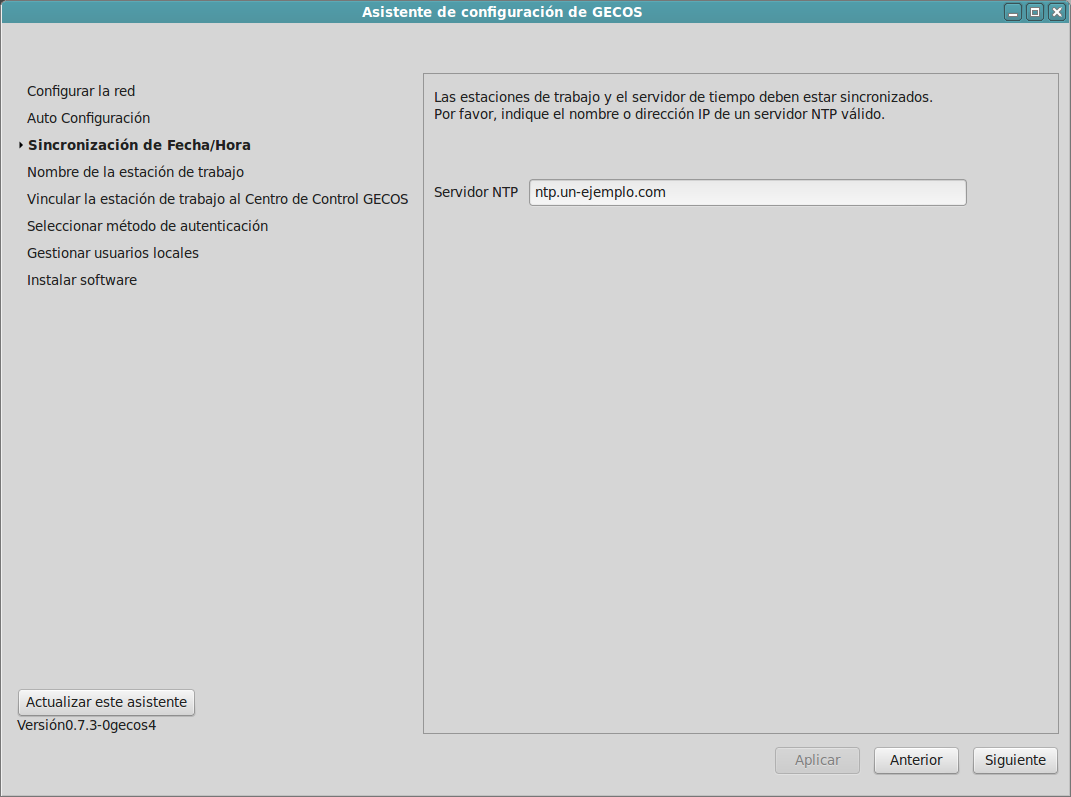
The right time
is essential for desktops and servers to communicate in a reliable way.
Provide the address of a Network Time Server (NTP) that your desktop computers can reach.
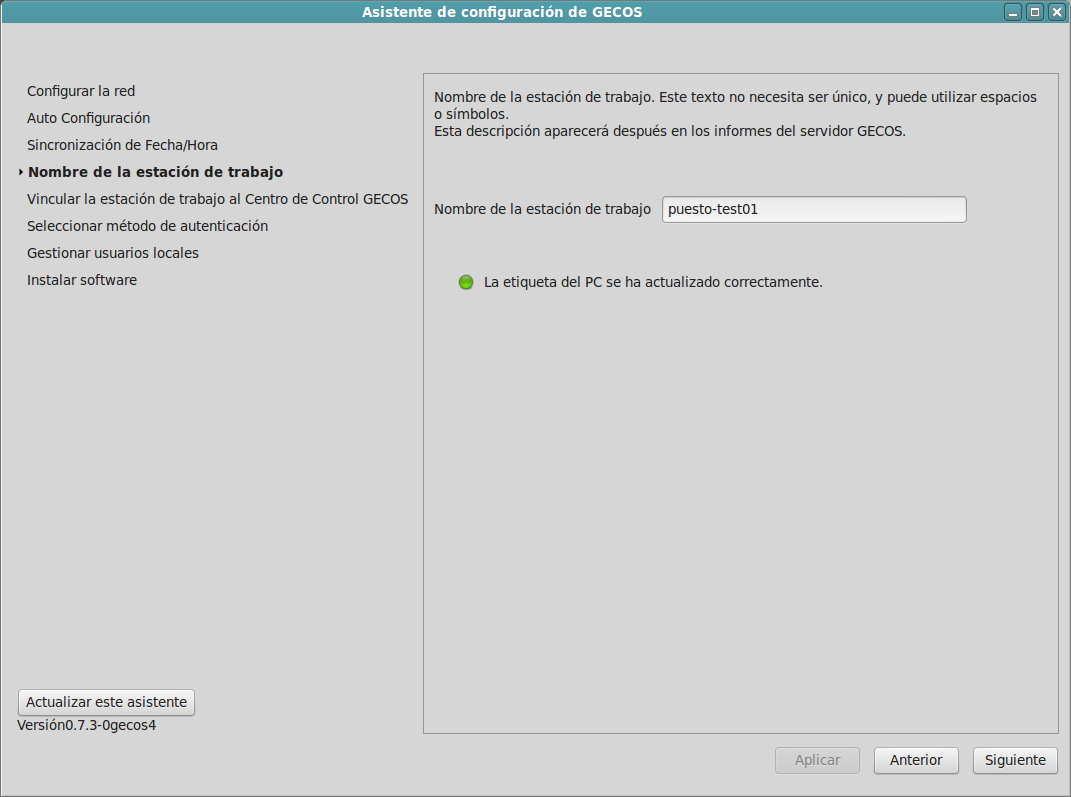
Identify
the computer with a name or code.
This name will be used by the Control Center to identify the computer.
The name must be unique within your organization.
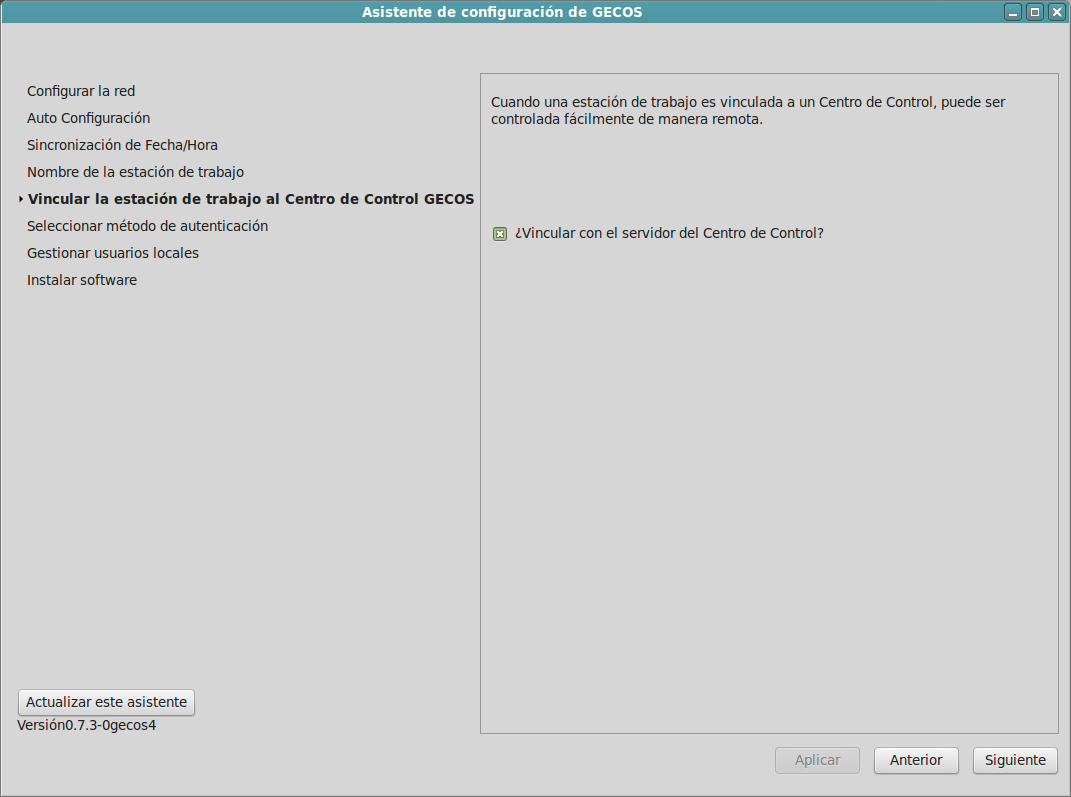
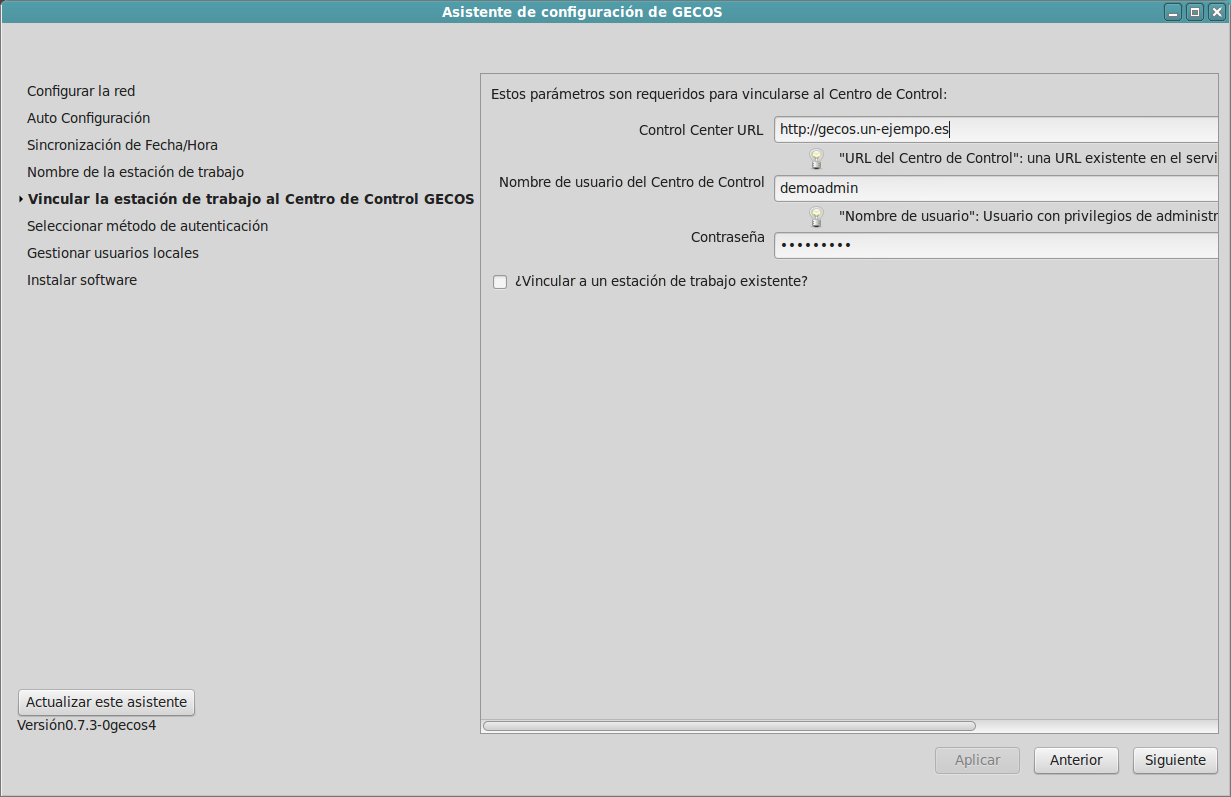
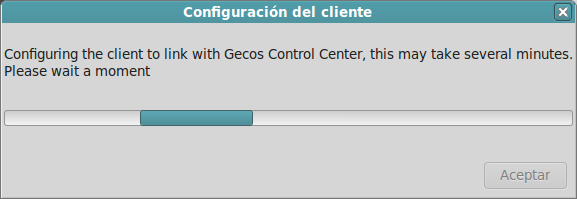
Attaching
the desktop to a Control Center allows you to configure, monitor, inventory... without moving around, just from your computer or tablet.
If you need it, you can have unattached GECOS computers.
Follow
to the next screen, the assistant completes the form automatically .
Don't check the last field unless you are re-attaching a desktop to the Control Center.
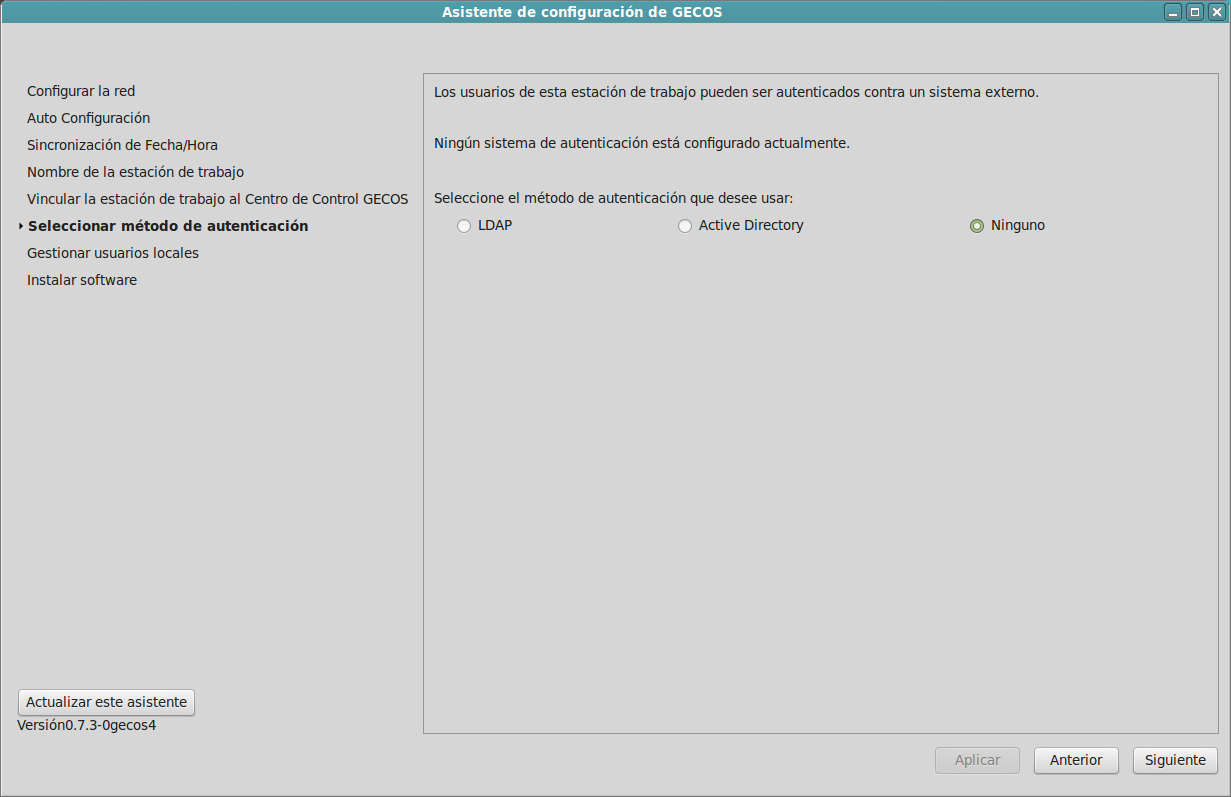
¿LDAP
or Active Directory?
A GECOS desktop can authenticate users by either system.
Or you can create local users without external authentication.
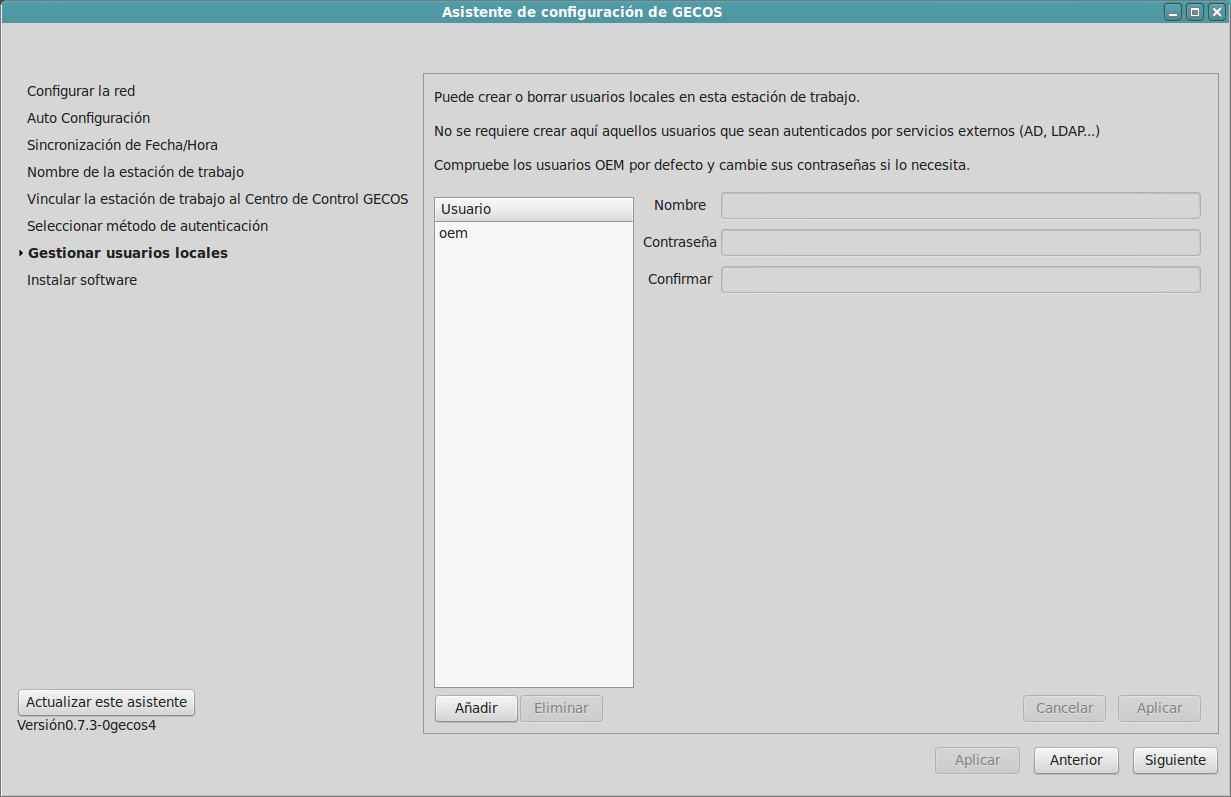
Local users,
to provide tech support, for emergency cases, or where no centralized authentication is available.
You can add users now, or much better, skip this and do it from the Control Center.
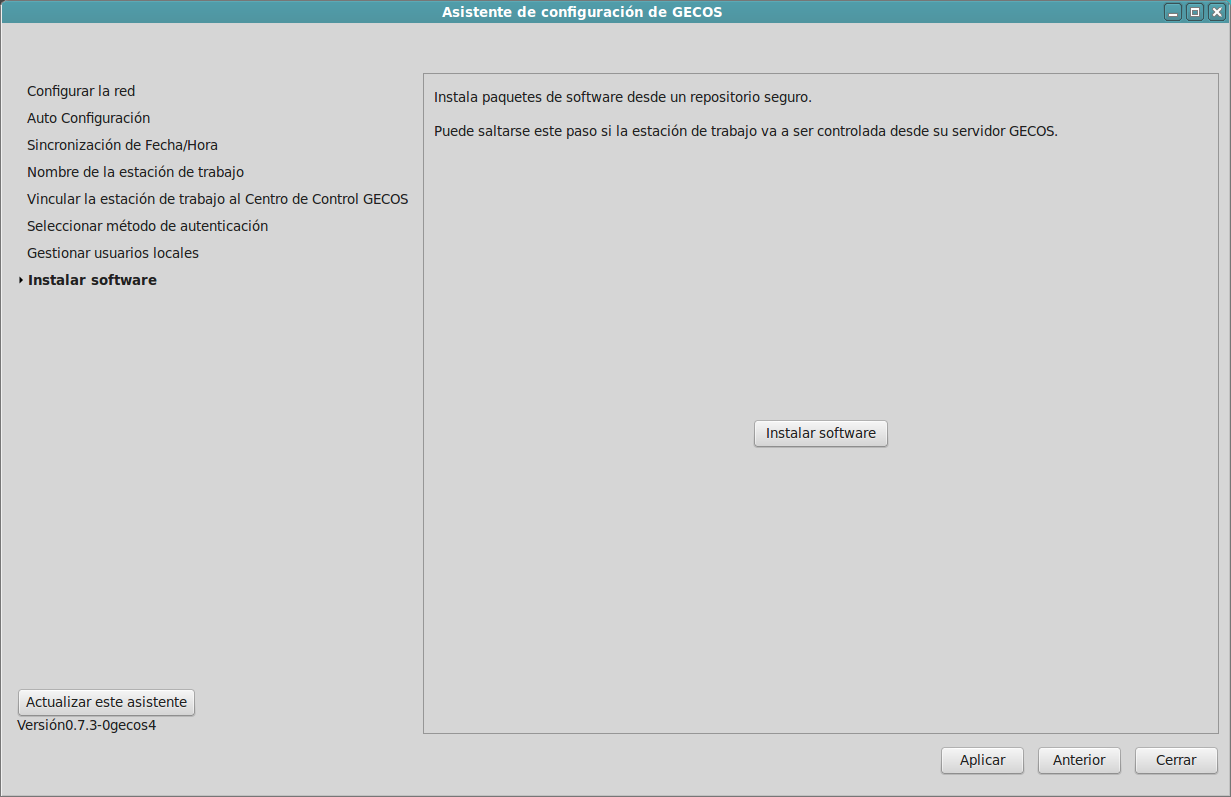
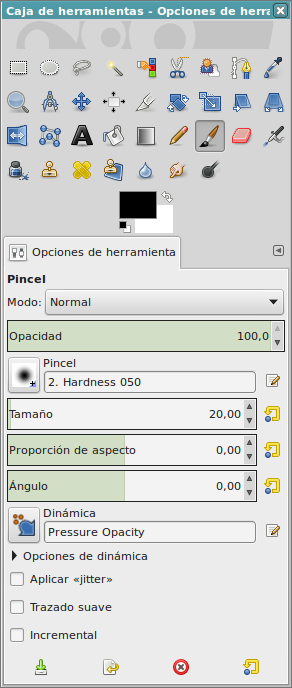
Applications,
utilities,
drivers,
fonts...
You can install them now, or you can complete the attachment process and do it from the Control Center.
Don't forget to press Apply before Exit.
Attached!
In a few seconds, the Asistant will have configured the desktop, put it under the management of the Control Center and connected it to the authentication system.
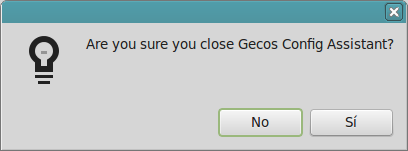
Exit the Assistant, and...
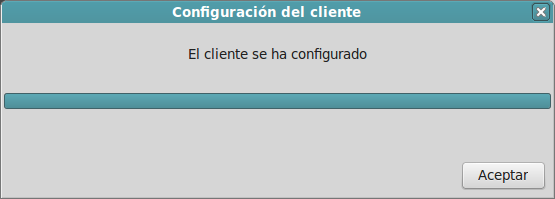
Enjoy centralized remote management!
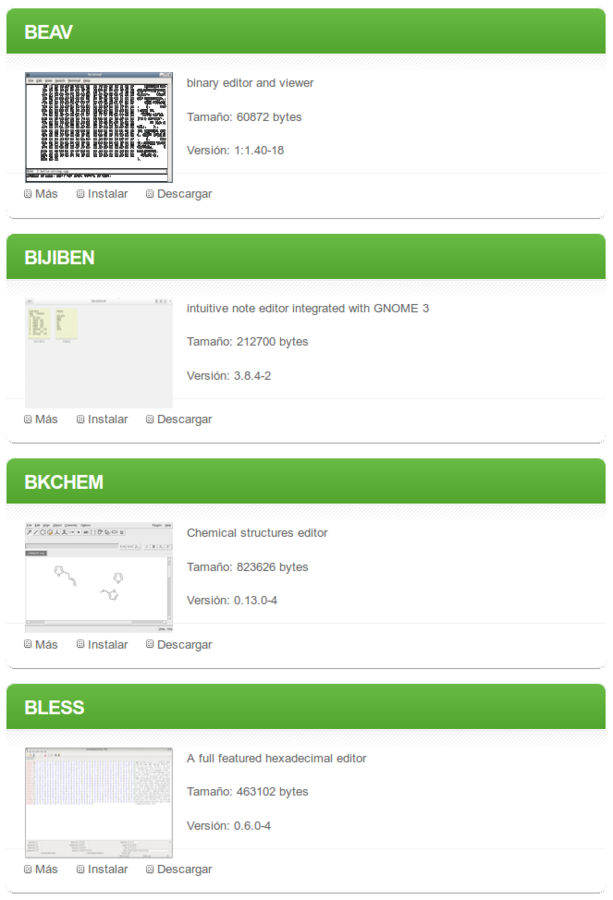
A software catalog
including:
- drivers
- fonts
- configurations
- manuals
- ...
Supervised, tested, and malware/virus free.

Applications
under free licenses, that you can install without per user or per desktop fees


Classified
in a supported repository that's periodically updated.
You can add your own repositories for privative or restricted software.
One system to rule them
ALL!
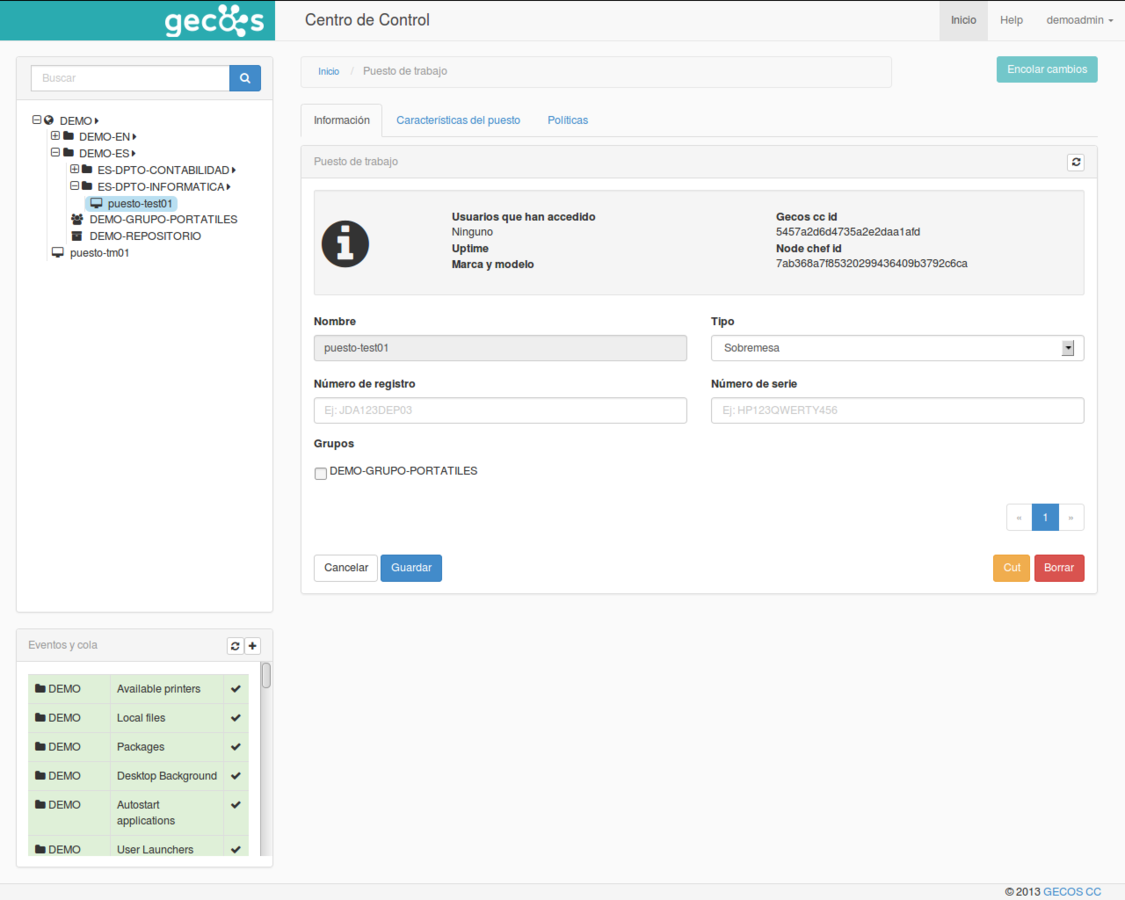
GECOS Control Center
Simple in the outside, but complex inside.
Based on standars, and well-known, reliable, free open source products and frameworks.
Pyramid
Celery
Chef
MongoDB
Nginx
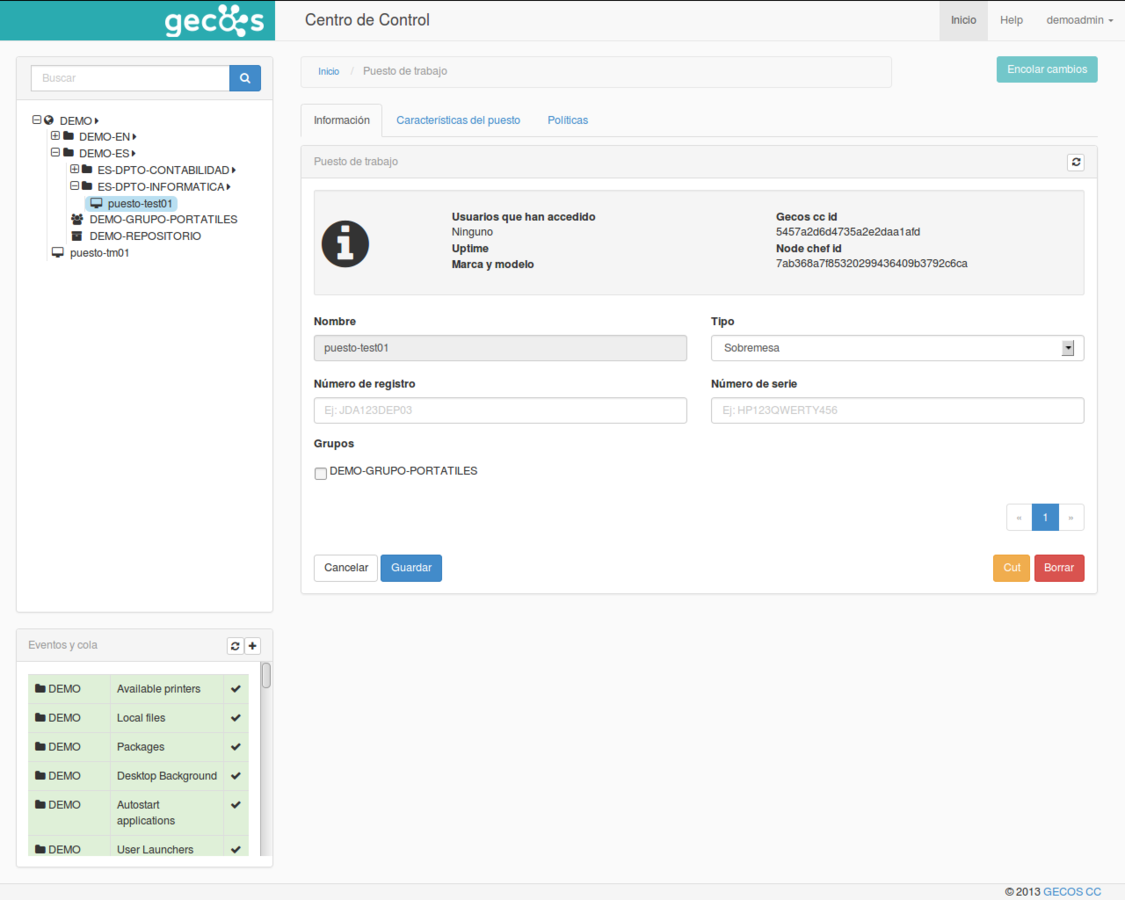
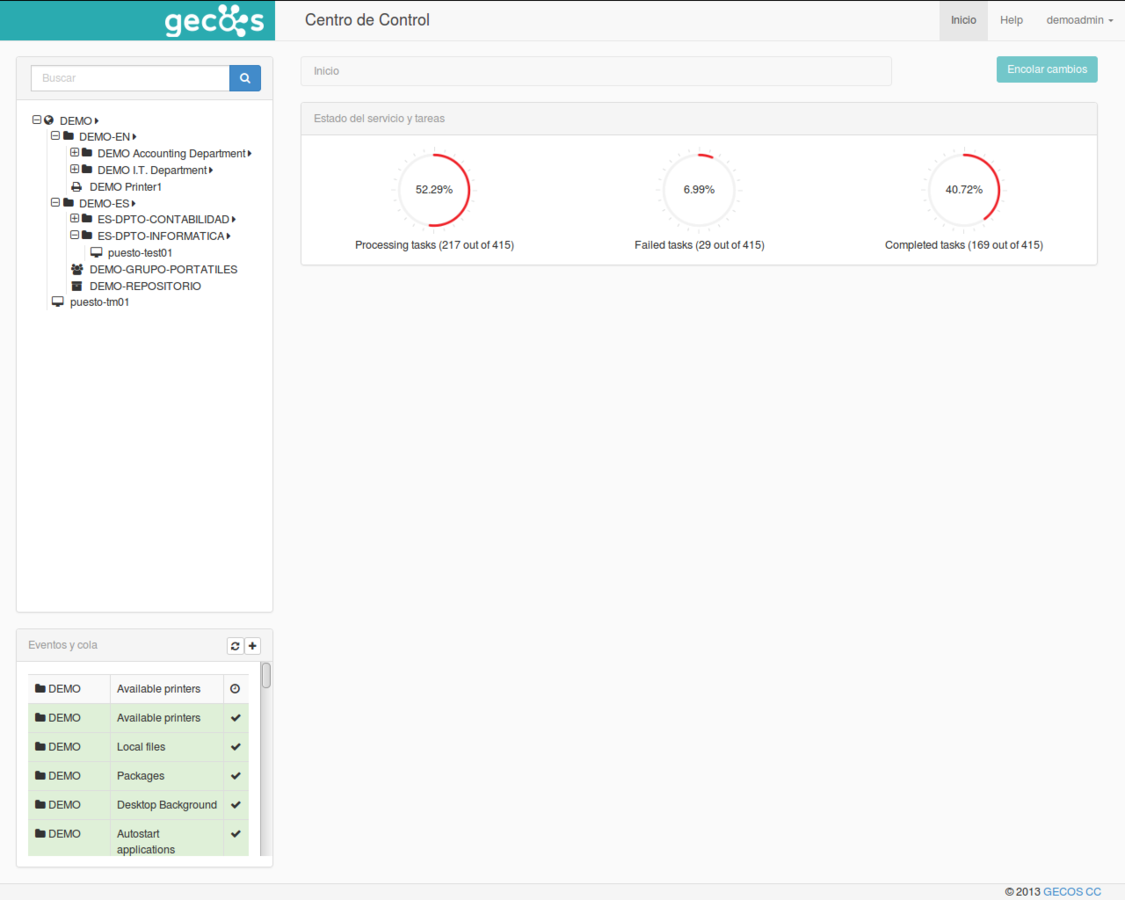
Your organization
clearly seen in the hierarchy tree on left panel.
You can create delegate administrators for selected organizational units (OU).
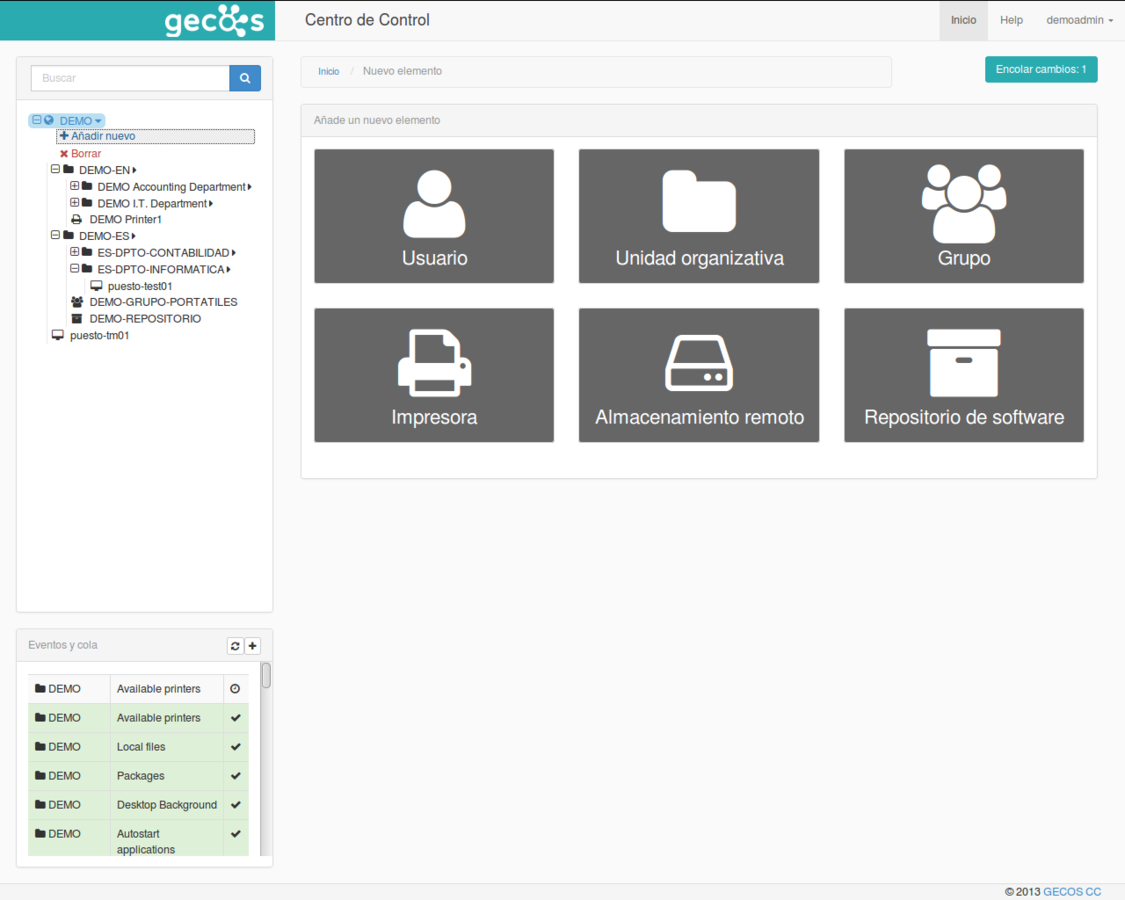
Manage
computers, users, groups and organizational units, storage, printers or software repositories.
From a homogeneous and friendly web interface.
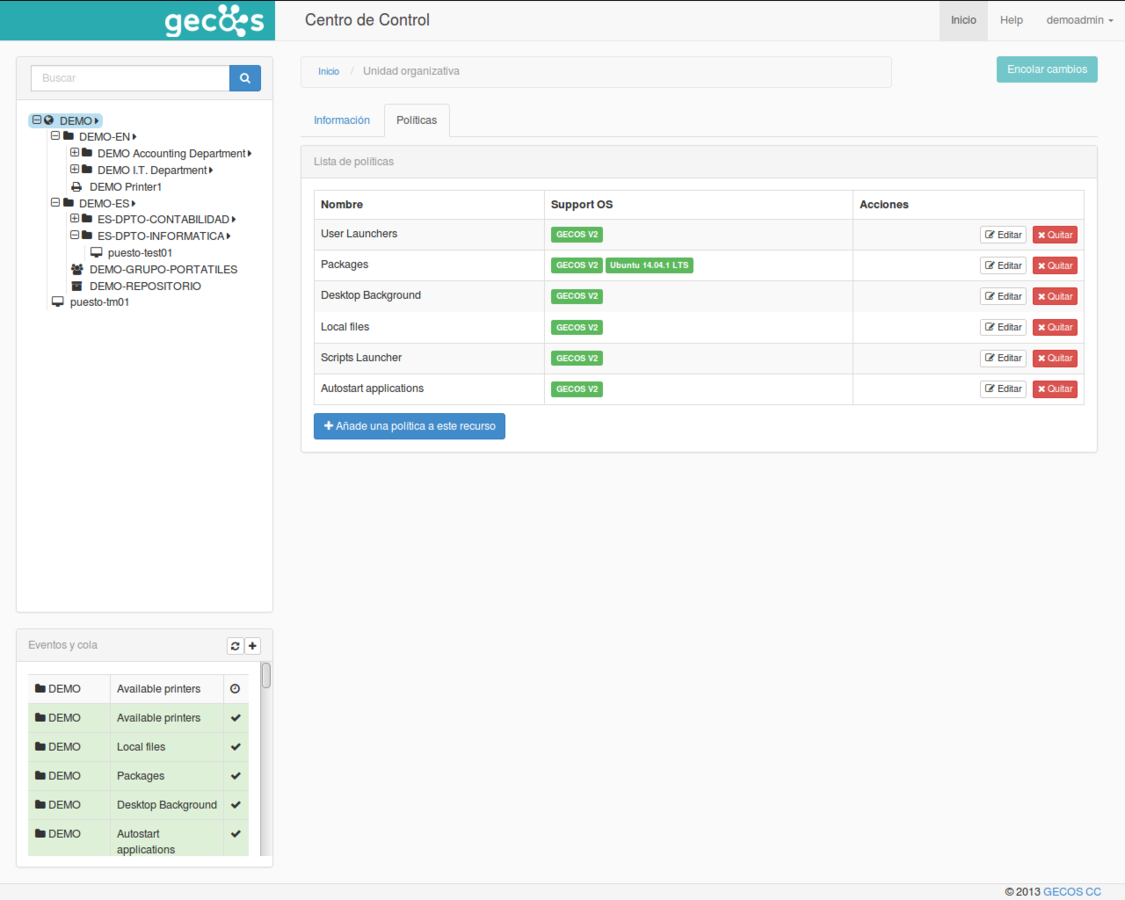
Policies
range from installing software, to changing desktop background, or blocking the use of USB drives.
Apply policies to single desktops or users, or to groups or organizational units.
You apply policies and GECOS enforces them.
Apply
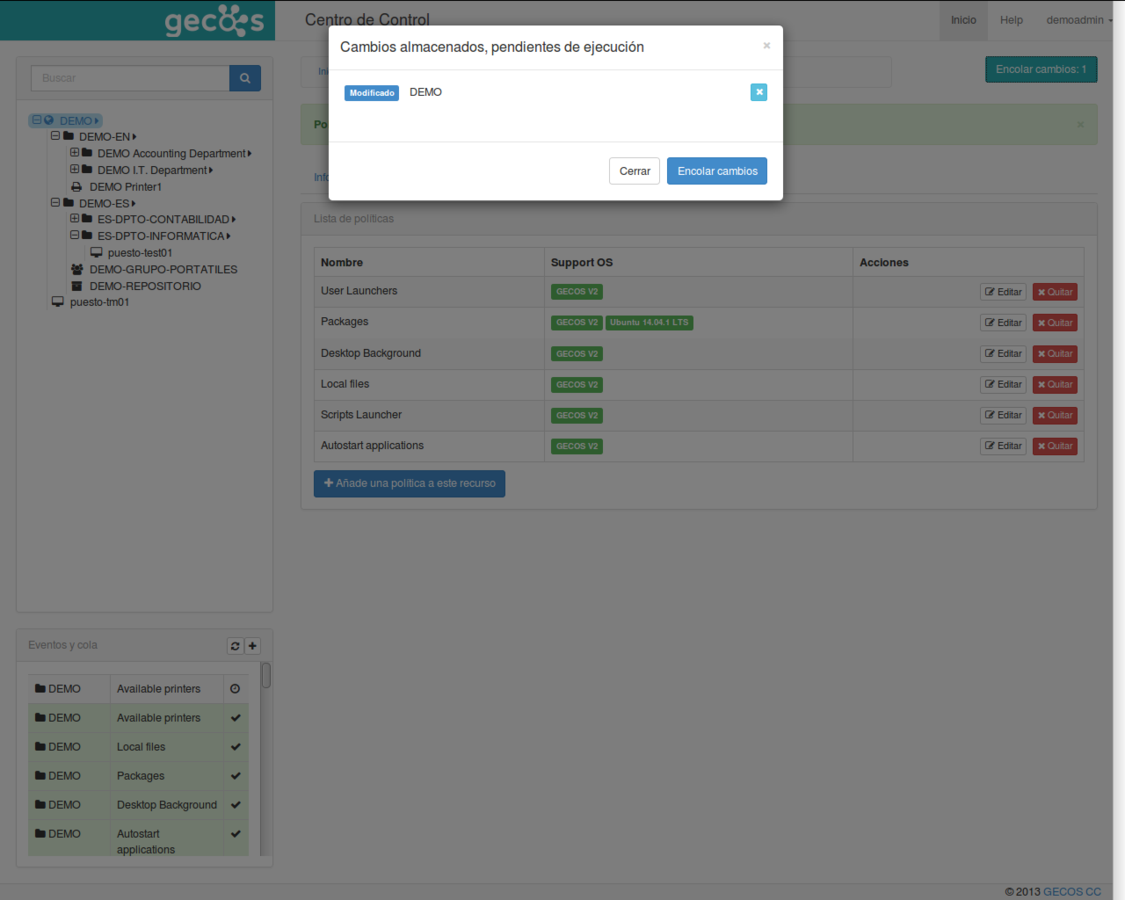
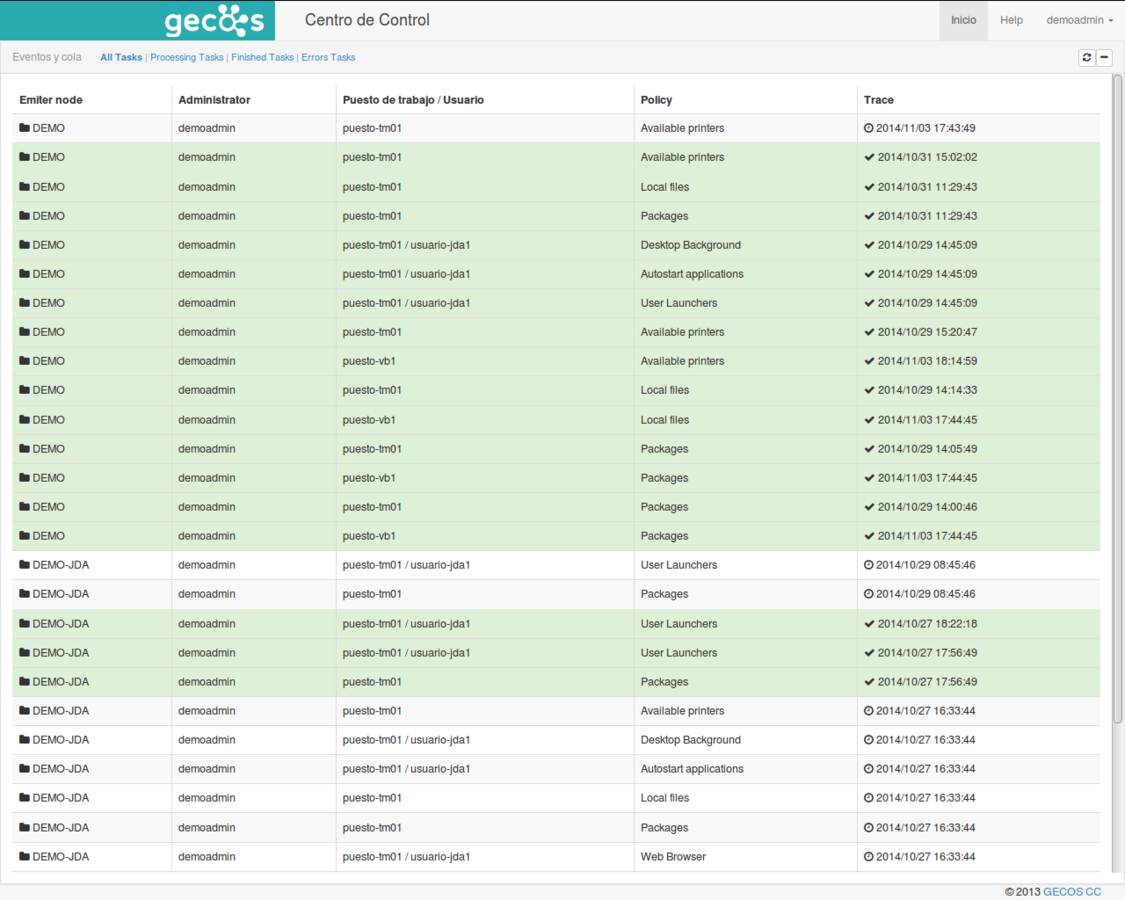
and check
Manuals,
support, source code, community...
gecos@guadalinex.org
http://https://github.com/gecos-team/gecos-doc/wiki